introduction: for small and medium-sized sites, security and cost are often contradictory. by rationally selecting and deploying high-defense us free virtual servers, you can improve your anti-ddos and intrusion prevention capabilities within a limited budget, while taking into account access speed and compliance. this article focuses on practical strategies and is suitable for webmasters and operation and maintenance reference.
why small and medium-sized sites need high-defense us free virtual servers
small and medium-sized sites face problems such as wide attack surfaces, limited budgets, and traffic fluctuations. choosing high-defense us free virtual servers can take advantage of the bandwidth and routing advantages of overseas nodes while maintaining node availability, reducing the risk of business interruption caused by attacks, improving the international access experience and dispersing single points of failure.
how to evaluate the security capabilities of high-defense us free virtual servers
when evaluating, focus on the protection mechanism, traffic cleaning capabilities, and visible log and alarm interfaces. confirm whether automatic traffic cleaning, rule-based protection, and black-and-white list management are supported, and audit logs can be exported to track abnormalities. also pay attention to whether the node provides a quick switch or rollback mechanism to reduce the risk window.
key points of network layer and application layer protection
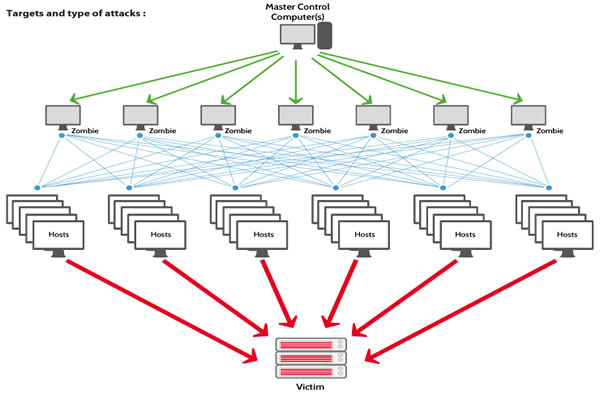
the network layer needs to have large traffic cleaning and rate limiting, and the application layer needs to support web firewalls, abnormal request detection, and anti-crawler strategies. combining cdn, reverse proxy and waf, malicious traffic can be intercepted at different levels to achieve "early filtering and layered protection" and improve the overall anti-attack capability.
deployment and migration practice suggestions
when deploying, it is recommended to verify the configuration in the test environment and make backups, and use grayscale switching or dns offloading to reduce risks. configure ssl/tls, force http to https redirection, enable minimum privilege accounts, and export key logs to secure storage or siem to ensure rapid location and recovery in the event of a failure.
cost savings and operations optimization strategies
when making reasonable use of free high-defense resources, it is recommended to combine a hybrid architecture: core business is placed on stable paid hosts, and peripheral traffic and burst protection use high-defense us free virtual servers or free cleaning channels. maximize cost-efficiency without sacrificing security through traffic distribution, caching policies, and on-demand start and stop.
compliance, performance and geo-optimization considerations
when choosing a us node, pay attention to data compliance and privacy policies to ensure that sensitive data has a compliant storage path. monitor latency and bandwidth at the same time, and use geographical routing or any available geo optimization methods to balance international access performance and compliance requirements to improve user experience.
summary and suggestions
summary: it is feasible to use high-defense us free virtual servers to save costs and improve security for small and medium-sized sites, but strict evaluation and layered deployment are required. it is recommended to conduct risk assessment and small-scale testing first, combine cdn/waf and log auditing, and adopt a hybrid architecture and on-demand strategy to achieve both stability and security within a limited budget.